

While the world marvels at the possibilities of quantum computing, an impending storm looms over traditional cryptographic systems. The rise of quantum computing has sent shockwaves through the cybersecurity realm, challenging the very foundations of data protection. As this cutting-edge technology surges forward, the vulnerabilities it poses to established encryption methods is concerning.
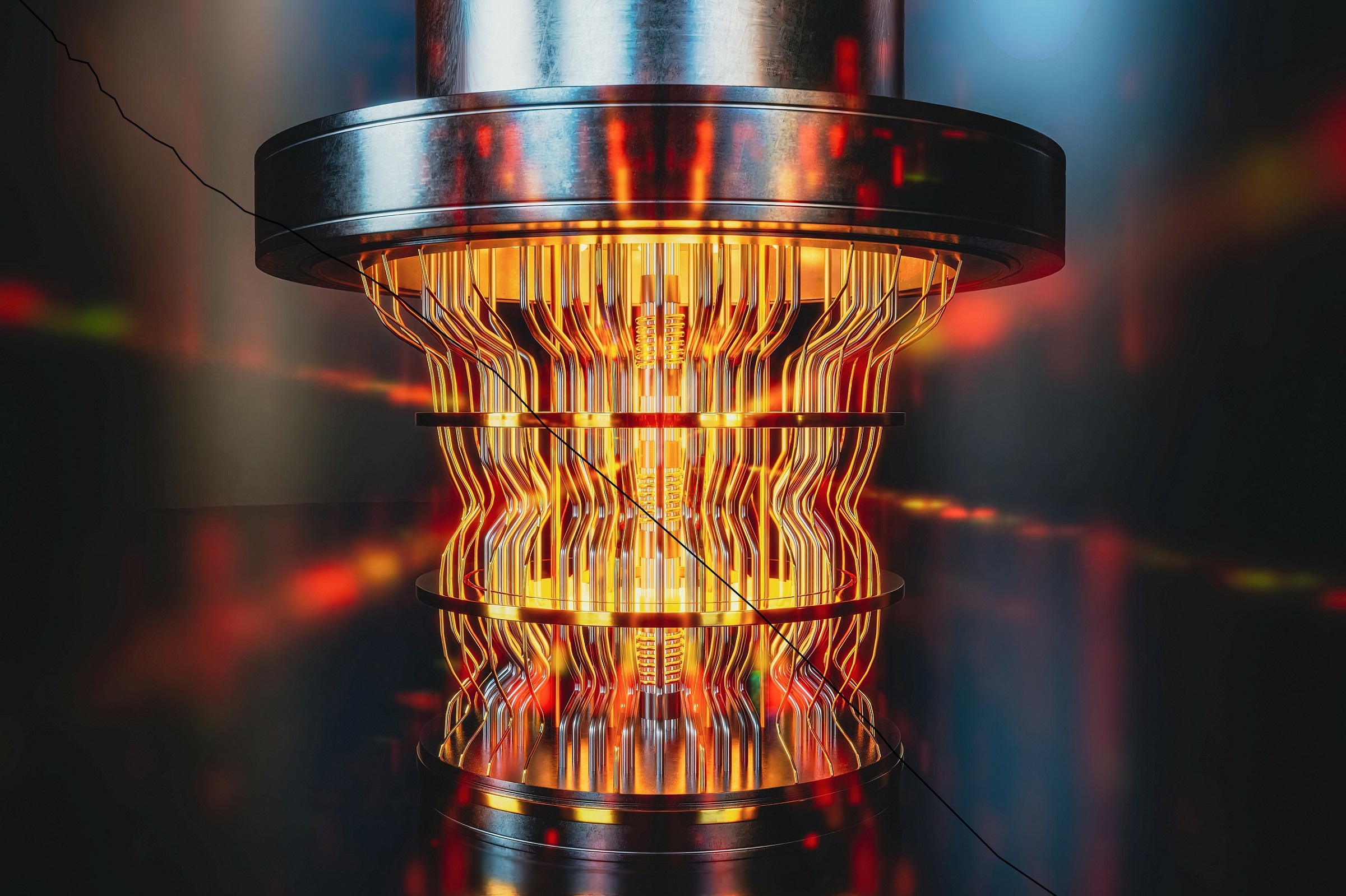
Quantum computers leverage quantum bits, or qubits, which can exist in multiple states simultaneously, allowing for parallel processing and the ability to perform computations at an exponential speed compared to classical computers. This breakthrough in computing power raises worries about the vulnerability of current encryption algorithms, which could be easily broken by powerful quantum computers.
Post-quantum cryptography (PQC) is an emerging field that focuses on developing encryption algorithms resistant to quantum attacks. Research efforts are underway to identify and standardize quantum-resistant cryptographic algorithms to ensure the security of sensitive information in the future quantum era.
Exploring the implications of quantum computing on cybersecurity and the ongoing efforts to develop quantum-resistant encryption can be a fascinating and timely topic that goes beyond the mainstream discussions surrounding more conventional cybersecurity issues.
While quantum computing offers tremendous potential, it also presents several significant threats to cybersecurity.
It is important to note that while these threats are anticipated, the exact timeline and impact will depend on the development and widespread adoption of practical quantum computers. Efforts are underway to develop and implement quantum-resistant encryption algorithms to mitigate these threats before they become a reality.
Stig Ravdal is the President & Founder of Ravdal, Inc., a leading cybersecurity strategy and solutions company. He is widely considered an expert in the field and is available for speaking engagements.
Continuous Penetration Testing is one of the most effective ways to safeguard your systems and data. Click here to learn more about Continuous Pen Testing or to schedule a call now.